Through Microsoft Dynamics 365 Sales and Microsoft Dynamics 365 Marketing global cloud communications company Infobip has integrated its SMS and WhatsApp channels. Now, it can help businesses boost sales, increase loyalty and deepen customer relationships. Last year,
Summary All over the world, the COVID-19 pandemic has completely changed working habits. Remote Working is basically any work done away from a physical office location. Remote work provides flexibility to all employees. They can be connected
In 1990, 31 years ago, Microsoft Office was initially released. Microsoft 365 (formerly Office 365), can improve your business efficiency, communication, and workflow when it comes to a productivity suite. Microsoft Office 365 comes with dozens of
In 2022, for most organizations preventing cyber-attacks is a top security concern. This year ransomware damaged the daily life all of us. Day by day attacks is growing steadily in size and sophistication. One of many major
You’re probably not going to be entirely aware of every feature it has to offer, unless you spend hours researching all the ways to use your new device. Specially, in the case of products like laptops and
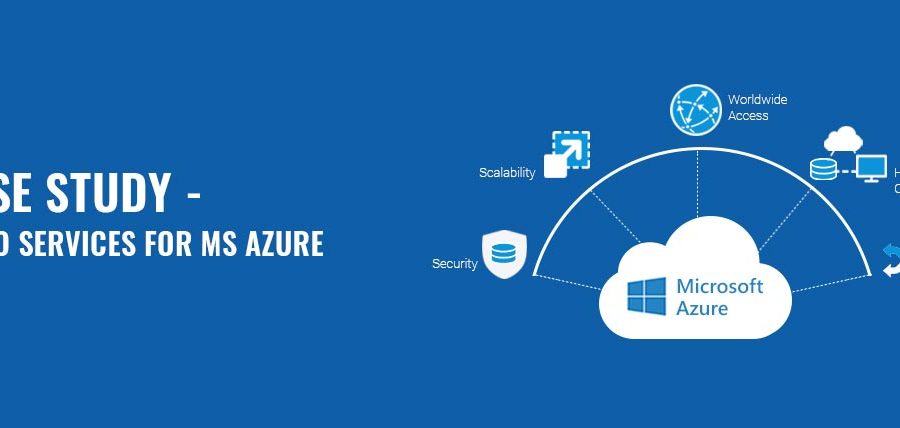
Summary Datto Services for MS Azure is a total business continuity and disaster recovery (BCDR) solution. You can predict these costs easily. You might have probably go-through a misconception that backup is not required for the data
Car companies are welcoming new mapping technology which will change the process you find destinations. It also saves your time as well as life. Jaguar Land Rover adds 3 words to their in-car navigation features. Mercedes-Benz, Tesla,
What is an SQL Injection attack? A SQL injection (SQLi) is a type of attack which is consist of the injection or insertion of a SQL query from the client to the application. Basically, it is a
First of all, we have to know what a brute force attack is. It is basically a trial-and-error method. Hackers mainly use this for encryption keys, to find a hidden web page, to crack passwords, or to
BP data migration process is the combination of selecting, preparing, extracting, and transforming data. It permanently transfers medical data from one computer storage system to another. Basically, it is the process of moving data from one application









Recent Comments